Chinese-linked Muhstik botnet targets Oracle WebLogic, Drupal
By MYBRANDBOOK
A security firm confirmed the Muhstik botnet, has been operating for at least two years, has recently started targeting vulnerabilities in the Oracle WebLogic application server and the Drupal content management system as a way to expand its cryptocurrency mining capabilities, according to the security firm.
Researchers earlier found that Muhstik targeted vulnerable IoT devices, such as routers, to grow its malicious network and perform other tasks, such as mining for cryptocurrency or launching distributed denial-of-service attacks.
The operators behind Muhstik are targeting vulnerabilities in web applications to increase the botnet's reach. This includes two vulnerabilities in Oracle WebLogic, which is used to help build and deploy enterprise Java EE applications.
Those flaws are tracked as CVE-2019-2725 and CVE-2017-10271One of the Oracle WebLogic vulnerabilities, CVE-2019-2725, was disclosed over a year ago, when researchers from Palo Alto Networks Unit 42 warned that it could be used to mine for cryptocurrency or deploy ransomware.
The Lacework researchers note that Muhstik continues to use the IRC protocol to communicate with its command-and-control server, which is fairly common for botnets.
Muhstik then attempts to download other malicious code within the infected device or web application. This includes the XMRig malware that is being increasingly used to mine for cryptocurrency, such as monero.
The botnet also attempts to download a scanning module that searches for other vulnerable applications or connected devices and then attempts to connect those to its malicious infrastructure, according to the report.
"Usually, Muhstik will be instructed to download an XMRig miner and a scanning module. The scanning module is used for growing the botnet through targeting other Linux servers and home routers," Chris Hall, a cloud security researcher at Lacework, notes in the report.
The researchers also found the Muhstik botnet leverages source code from the Mirai botnet. This includes a memory scraper, which can kill other malware within a device.


Nazara and ONDC set to transform in-game monetization with ‘
Nazara Technologies has teamed up with the Open Network for Digital Comme...

Jio Platforms and NICSI to offer cloud services to government
In a collaborative initiative, the National Informatics Centre Services In...

BSNL awards ₹5,000 Cr Project to RVNL-Led Consortium
A syndicate led by Rail Vikas Nigam Limited (abbreviated as RVNL), along wi...

Pinterest tracks users without consent, alleges complaint
A recent complaint alleges that Pinterest, the popular image-sharing platf...


Icons Of India : Arundhati Bhattacharya
Arundhati Bhattacharya serves as the Chairperson and CEO of Salesforce...

Icons Of India : CP Gurnani
Former Managing Director and CEO of the well-known IT service company ...
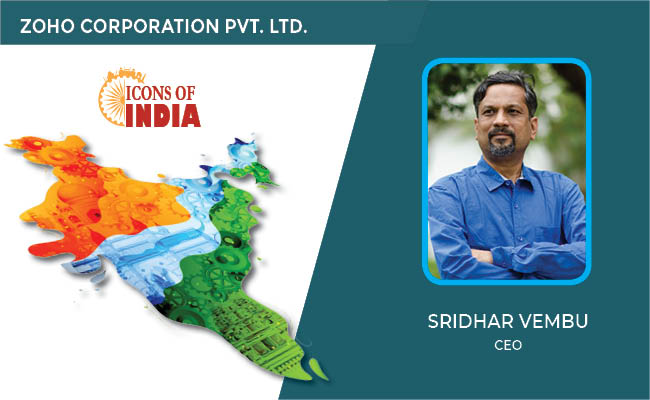
ICONS OF INDIA : SRIDHAR VEMBU
Sridhar Vembu is the chief executive officer (CEO) of Zoho Corporation...


IOCL - Indian Oil Corporation Ltd.
IOCL is India’s largest oil refining and marketing company ...

RailTel Corporation of India Limited
RailTel is a leading telecommunications infrastructure provider in Ind...

IREDA - Indian Renewable Energy Development Agency Limited
IREDA is a specialized financial institution in India that facilitates...


Indian Tech Talent Excelling The Tech World - Dheeraj Pandey, CEO, DevRev
Dheeraj Pandey, Co-founder and CEO at DevRev , has a remarkable journe...
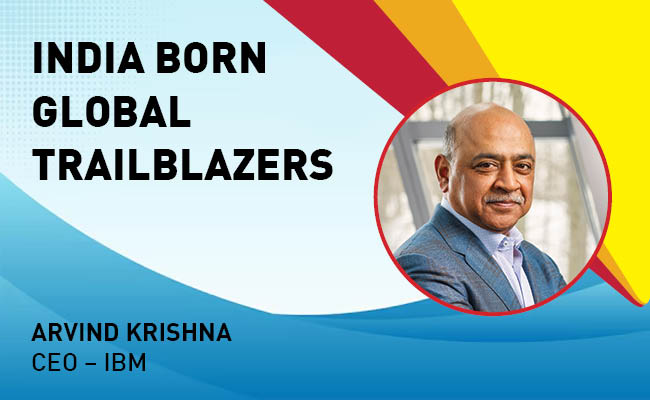
Indian Tech Talent Excelling The Tech World - ARVIND KRISHNA, CEO – IBM
Arvind Krishna, an Indian-American business executive, serves as the C...

Indian Tech Talent Excelling The Tech World - ANJALI SUD, CEO – Tubi
Anjali Sud, the former CEO of Vimeo, now leads Tubi, Fox Corporation�...